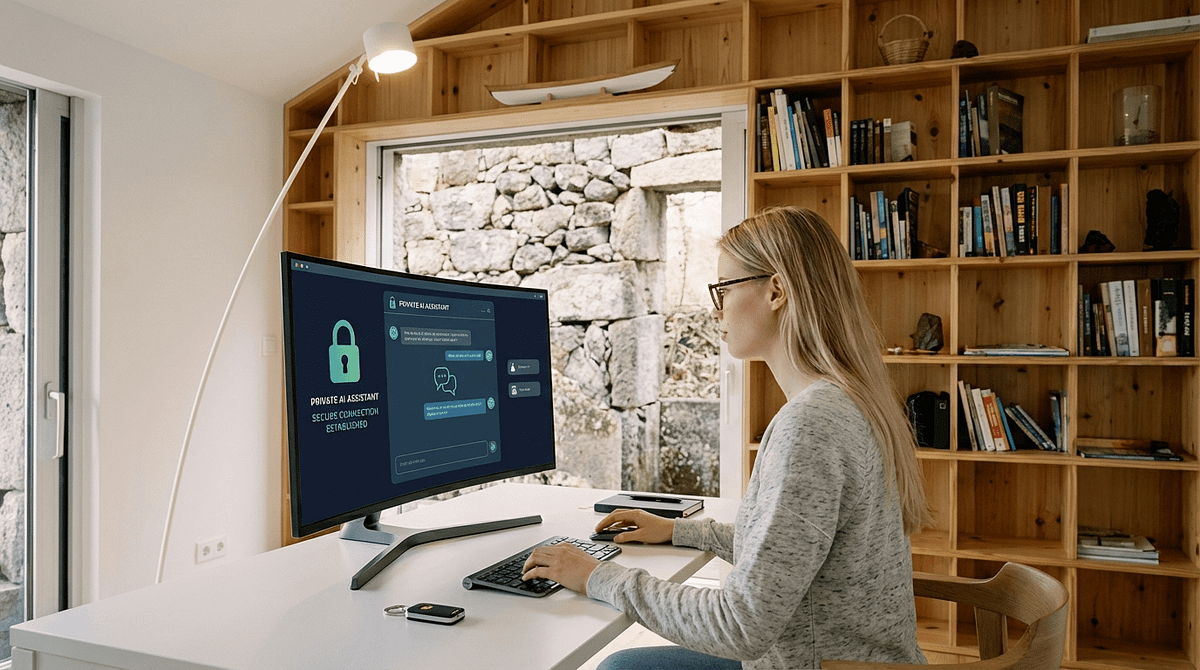
What if there were an online privacy solution that was much faster than Tor and, unlike VPNs, allowed no single third party to read encrypted information? That’s what David Chaum, an Internet security and privacy veteran, aims to implement through a new type of mixed network called PrivaTegrity.
PrivaTegrity is designed to work somewhat like Tor in that it would shuffle messages through a series of nine servers before delivering them to a recipient. The messages would be encrypted as they traveled between the servers, and they would go through several rounds of jumbling before reaching their destination.
Through this approach, no single server would be able to decrypt the message fully, and no one eavesdropping on the traffic would be able to identify its source or contents.
If free of flaws, PrivaTegrity would be better than Tor, which routes messages in a straight-forward fashion through only three proxies before sending it to a recipient. That method is not as robust as bringing nine proxies into the mix. Plus, with Tor, you run the risk that one of your proxies could be malicious and intercept your data.
PrivaTegrity would also be better than a VPN, which does not protect your online activity from the VPN provider itself.
Perhaps best of all, PrivaTegrity developers say it will be much faster than Tor. That’s because the method makes it possible for servers to do much of the thinking required to jumble a message’s contents ahead of time, rather than having to do it all on the fly, as Tor requires.
For now, PrivaTegrity remains a work in progress, with much coding still required to implement it. But its creator, Chaum — who was a pioneer of mixed networks and computer cryptography in the early days of the Internet — says an alpha version for Android devices is in the works. Stay tuned.






PrivaTegrity promises a compelling alternative to Tor by emphasizing speed and usability. However, users should evaluate their specific privacy needs, consider the reputation of each service, and stay informed about the evolving landscape of online privacy solutions.
Doesn’t Chaum also want to leave a backdoor in this project. Something about all 9 servers in different countries having the ability to cooperate and decrypt traffic if they agree to do so?