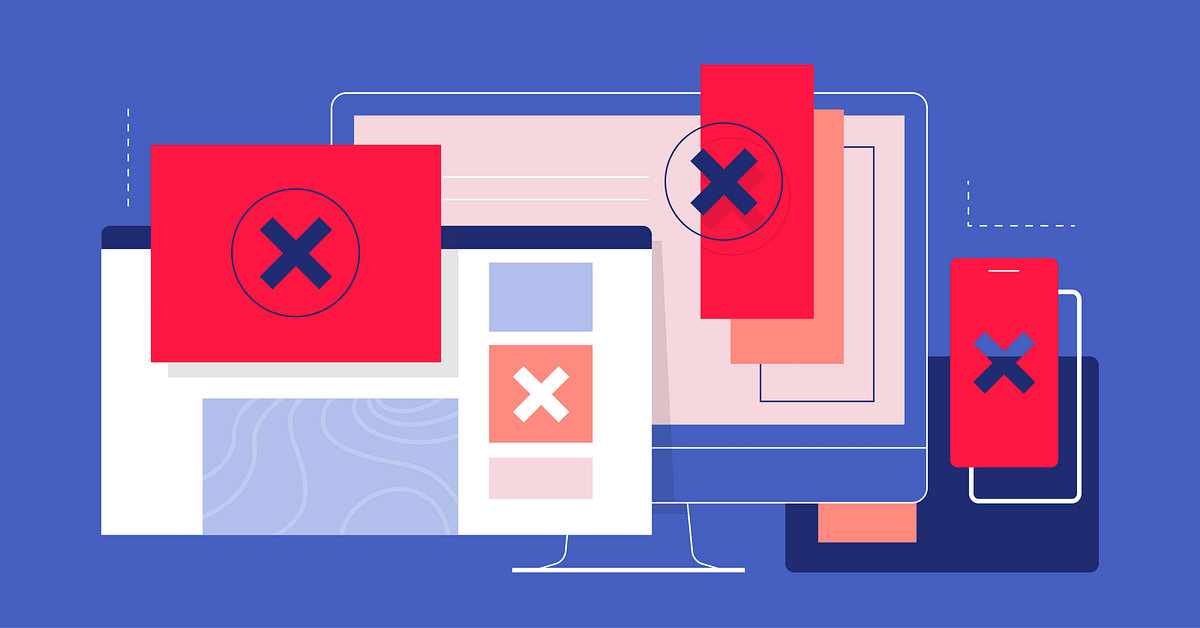
If you are using OpenVPN in China, even on port 443, you may find that your connections are unstable. The problem is that the Chinese government can detect the difference between “normal” SSL encryption and VPN encryption.
The solution is to mask your OpenVPN connection and make it look like a regular HTTPS connection.
You can do this using one of these methods:
- Using OpenVPN through an SSL tunnel
- Using OpenVPN through an SSH tunnel
- Using a tool called Obsfsproxy
- Masking the OpenVPN packets in other ways
Here are three VPN providers that support obfuscation:
- VPN.AC uses TLS authentication to mask OpenVPN handshake packets (thus hiding it from Deep Packet Inspection)
- AirVPN supports SSH tunneling and SSL tunneling by default
Note that OpenVPN obfuscation techniques will not work on Android devices or iPhones/iPad (yet).

Hosting Your Own VPN on a VPS
You may want to create your own VPS with an OpenVPN installation and obfuscation. I recommend using a reliable VPS like Vultr. You can install OpenVPN using a “one-click” interface, and they have servers in Asia, and see my article How To Set Up Your Own VPN.
Once you have the VPN set up, you can then install an SSL tunnel:
Using OpenVPN through an SSL tunnel
You can make your OpenVPN traffic virtually indistinguishable from regular SSL traffic by tunneling it through SSL because Deep Packet Inspection cannot penetrate this additional layer of encryption.
Typically, you’ll want to install the stunnel application and also install stunnel on your VPN server. Here are some more instructions for setting up stunnel. See this discussion.
Note that using an SSL tunnel will slow down your internet connection.
UDP is better for any kind of tunnel because it has lower overhead and doesn’t try to retransmit packets unnecessarily. In certain instances retransmitting packets could be counterproductive. Basically, anything that needs to either have a stateful connection or a connection that is “reliable” (i.e., TCP) already has packet retransmission built into the protocol. If you run two of these protocols on top of each other (such as TCP over a TCP tunnel), then bad things start to happen, as now you have more than one layer trying to retransmit packets. So really, you should use UDP unless there’s a very specific reason you need to use TCP, such as a firewall restriction or something.
OpenVPN through an SSH tunnel
Using OpenVPN with an SSH tunnel is very similar to using it with an SSL tunnel. The difference is that you wrap your OpenVPN traffic with SSH encryption instead of SSL encryption. SSH is the “secure shell” software used to connect shell accounts in Unix. You can find SSH clients for most operating systems — see PuTTY, for example.
When using SSH tunnels, note that:
- There is evidence that the Chinese government is slowing down SSH connections
- SSH is much more than just encryption. Therefore you will see more overhead with SSH tunnels
- SSH is difficult to set up on Windows, whereas stunnel is cross-platform
Using Obsfsproxy
Obfsproxy is a tool designed to make VPN connections difficult to detect. It was created by the Tor network when China started blocking Tor nodes — but it can be used outside of the Tor network to mask VPN connections.
There are instructions for setting up Obsfproxy with OpenVPN on this page.
Obfsproxy does not encrypt your traffic, but it also does not require much overhead, so if it is useful in countries where bandwidth is limited (e.g., Syria or Ethiopia).





**Great point about port 443 detection!** Since the Chinese government can distinguish VPN SSL from regular SSL even on the standard HTTPS port, I’ve found that using obfuscation tools like obfs4 is essential for maintaining stable connections. Does the article recommend any specific OpenVPN configurations to bypass this detection?
Great point about the port 443 instability — it’s frustrating that even standard SSL isn’t enough to fool the detection. Are you using a newer version of the obfuscation layer to mask the traffic patterns, or sticking with the default config?
**This is a critical issue for anyone trying to maintain privacy while traveling in China. The article’s point about China’s ability to distinguish VPN traffic from normal SSL connections on port 443 is especially important—I’ve noticed my own connections became unstable even when using standard ports. Have you found that switching to obfuscation protocols like obfs4 helps bypass these detection mechanisms effectively?**
Great overview of VPN obfuscation techniques! For those looking to host their own OpenVPN with SSL tunneling, check out https://z-image-turbo.me/ for reliable VPS options that work well with obfuscation setups.
This is super helpful! It’s wild how much effort goes into maintaining a stable connection in China. Dealing with DPI sounds really tricky.
Hopefully, this director will bring about change.
Very informative, good to know about SSL/SSH tunneling and obfsproxy for bypassing restriction in China
I would like to go to China for 3 months but I use OpenVPN for my work. Is there a way in 2023 to solve this problem without having a significantly reduced internet speed? Can I combine 2 VPNs?
I will settle in China next month. I plan to set up a virtual server on Digital Ocean with OpenVPN with STunnel. Typically, getting a reliable VPN connection in China is significantly more difficult. Hope that it will work flawlessly.
The article mentions that obfuscation on Android is not possible yet. Is this still the case in 2019? The article was written in 2017
I have the same opinion as you.
I recommend you try shadowsocks instead of a VPN if you are setting up your own server on a VPS. It works much better than any of the obfuscation methods mentioned on this page. You can find a tutorial here.
https://www.tipsforchina.com/how-to-setup-a-fast-shadowsocks-server-on-vultr-vps-the-easy-way.html
I just returned from a trip to China (Nanjing and Shanghai) for the whole month of April 2016. I had set up a virtual server on Digital Ocean with OpenVPN with STunnel. Nanjing is usually a much tougher place to get a good VPN connection. But it worked flawlessly. I had better performance than any commercial VPN service I ever used.Not the fastest (but faster than the commercial services I used) but good enough to stream youtube It was just a bit tricky to get it set up right but once I did it was great. The only thing I noticed was after the first connection from China, every time I tried to log into my DO server through their terminal I was greeted with the message that there were thousands of unsuccessful login attempts from an IP behind the Great Firewall. So the GFW people were also interested in logging into my server. Make sure you have a nice big secure Password and set up your firewall. From the graphs it looked like some program was trying to login every 30 minutes to an hour. Most of my setup time was spent debugging performance before going, until I figured out (and verified online) that FIOS was throttling my VPN over UDP. Once I switched to TCP things went faster (I needed to do that anyway for the STunnel setup).
I will settle in China next month. I plan to set up a virtual server on Digital Ocean with OpenVPN with STunnel. Typically, getting a reliable VPN connection in China is significantly more difficult. Hope that it will work flawlessly.
Most of my setup time was spent debugging performance before going, until I figured out (and verified online) that FIOS was throttling my VPN over UDP. Once I switched to TCP things went faster (I needed to do that anyway for the STunnel setup).
NC, the problem is – your server software and client software MUST also be specially coded for such strictly banned environment.
Who would like to do this instead of subscribing a ready-made plan? Time is Money, right?
If I have access to homes in other countries, can I setup a vpn server using raspberry pi? What would I have to do to go around the gfw? I wanted to use openwrt as my client at home. But also hoping to access the vpn on my ios device using china Unicom.
Why don’t you try Dante Socks SSH Tunnel or Microsoft SSTP? A very straight forward solution to bypass censorship. Very few company provides this service.
You can try , a Hong Kong registered company run by British person.
https://2vpn.co/
I am actually using Greenvpn right now, it works really well, my internet connection reaches 44M at download bandwidth, but only 2M at around the upload bandwidth, fairly enough for me.
A good combination of VPN and SSH(obfuscated of course) may fool GFW as the wall in BattleField 4– completely destroyed. LOL. What’s more, don’t forget both Tor and I2P.
hello, I am Chinese, and we Chinese love dnsmasq on OpenWRT router very much. Dnsmasq with an obfuscated SSH can make a better performance against GFW.
Is it a must to combine OpenVPN with an SSL/SSH tunnel?
It is possible to let’s say create a SSL/SSH tunnel and send the communication through this tunnel to a proxy server set up in your VPS? What I’m probably wrongly supposing is that as long as you have an encrypted tunnel you don’t actually need to encrypt the data passing through it… or in other words why double encryption (i.e. OpenVPN + SSH/SSL) is necessary to circumvent the firewall?
The SSL tunnel is ued to camoflague your VPN connection, so it is indeed a redundant layer of encryption, and it does slow down your VPN connections. It’s for the sake of obfuscation.
I really agree with you. The SSL tunnel iss indeed a redundant layer off encryption, and it does slow dowwn your VPN connections.
I recommend Linode. The best VPS provider for Customers restrained in China.
Thank you for the recommendation. I’m glad to hear that Linode is working well for you.
My experience running openvpn connections through both stunnel and ssh is that the connections are good for about 10-15 minutes. The connections are not terminated, but after about 15 minutes the speeds get throttled down to unusably slow. Of course YMMV depending on where you live in China, but these types connections are certainly not undetected. On the other hand, these methods are nice in a pinch one needs short term connectivity and nothing else works.
Additionally on:
“ExpressVPN uses a confidential method of packet obfuscation”
I find ExpressVPN to be a reliable provider, but its implied that openvpn connections through their service are undetectable. That’s not my experience — inability to connect and broken connections are a daily experience. Don’t interpret that negatively, I have yet to find a provider that is trouble free, ExpressVPN is fine and offers quite a bit of connection choices, and, again, ones experience depends on where one is connecting from.
Lastly, my experience setting up vpn servers on DigitalOcean is that they work great for a time until they are tracked down, after which one will never connect to that DO ip again. If I do another setup there I would probably additionally setup a firewall so that the server only responds to connections from my home ip. The intent there being to make it more difficult for automated probing to identify much about the server, and so less likely to clobber connections to it and risk collateral damage. Ultimately, though, I have not done the experiment yet to find out what happens and how to counter it…. ;(
I finally got around to experimenting a bit with external servers and the great firewall. What I notice is that as soon as ssh connections are initiated to my external server. The server starts getting probed, approximately every two minutes, by servers owned by China Telecom in JiangXi and China Unicom in HeBei. The probes cant find out anything out about the server, as all connections except those from my home address are being dropped. The resulting connection is stable but interestingly enough seems to be, none the less, rate limited. The connection speed is fine for command line based server managment but not suitable for higher bandwith usage scenarios.
In view of the real time response of the firewall to encypted connections to end points outside of the country, I am not terribly optimistic about some of the “do it yourself” suggestions above. I suspect that while we can encrypt our connections or disguise them as something else, those connections are likely to be fragile in the medium to long term. Its perhaps less hassle and a longer term more successful strategy to just hire the full time, private vpn companies fight this battle against what is a very capable, and well funded, adversary.