Tor is probably the best known all-around Internet privacy solution. But I2P, another open-source framework for secure, censor-free communications, offers many of the same features as Tor and may be better in some situations.
I2P’s promise is to provide “strong privacy protections for communication over the Internet. Many activities that would risk your privacy on the public Internet can be conducted anonymously inside I2P.”
The free and open-source platform, which was first released in 2003, lets users send information over the Internet anonymously. Like Tor, it creates a decentralized overlay network where users’ identities can’t be determined, and sends Internet data over that network.
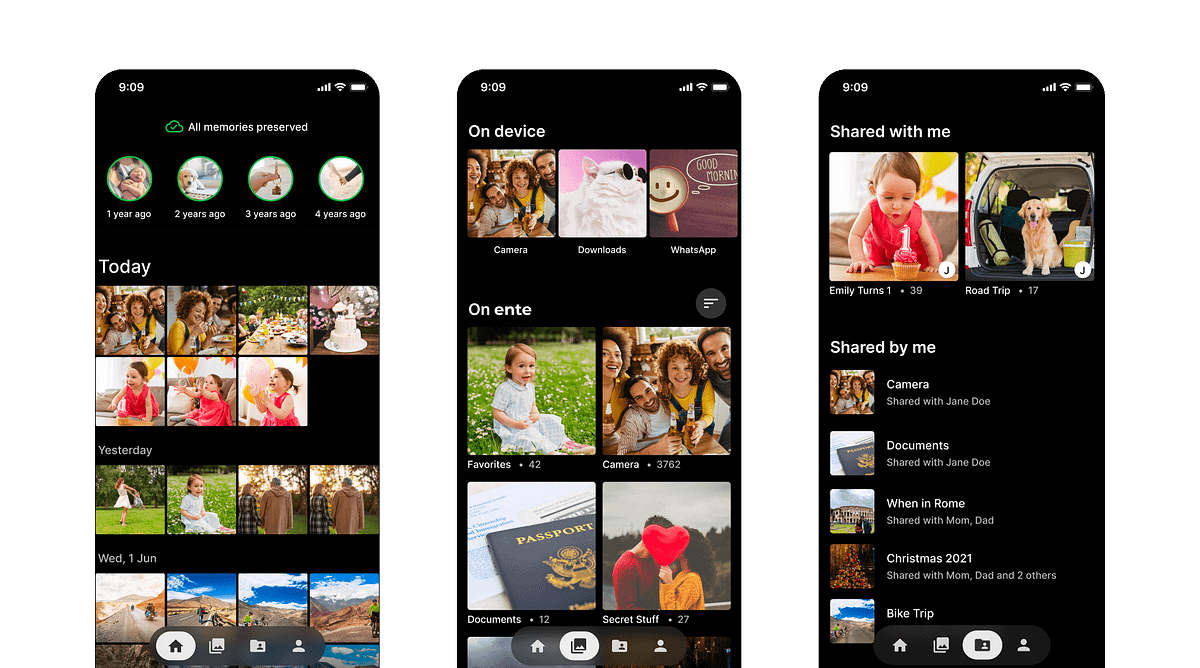
Also like Tor, I2P is a general-purpose Internet anonymity solution that supports all kinds of Internet messaging. It can encrypt and anonymize chats, emails, file sharing, instant messaging and all other kinds of normal online activity. It’s not limited to particular protocols.
And, since I2P runs at the network level, it protects all network activity. It’s not restricted to a certain app, as would be the case with privacy extensions for your Web browser, for example.
The I2P developers recognize that their platform does many of the same things as Tor, and they state that Tor has several advantages over I2P. Those include things like more funding, more users (which means more nodes for circumventing online censorship) and lower bandwidth overhead in Tor apps.
On the other hand, I2P also offers advantages over Tor, including:
- Being less widely used than Tor, which means it is not as frequently targeted for blocking by censorship authorities.
- Packet-switch networking design, which helps balance bandwidth loads better and provide more redundancy for communications.
- Other “peers” in the network — that is, nodes through which information passes to circumvent censorship — are continually reevaluated, rather than permanently trusted by the system.
- Because I2P was designed from the ground-up for running hidden services, they work “much faster than in Tor,” according to the I2P developers.
Officially, I2P remains beta software. That’s perhaps another disadvantage compared to Tor. But, in the right situations, it may be a handy alternative for beating censorship and staying private online.