ICLOAK recently launched its plug-and-play online privacy solution, which is based on a custom Linux distribution that boots from a USB stick. We contacted the company to get a better sense of how exactly its privacy features work, including Tor integration, VPN availability and more.
This is what ICLOAK founder Eric Delisle said in response to questions about the product’s technical features:
How do Tor and other proxies work in ICLOAK?
We built a network controller which at this time manages 1) Tor and 2) a local Privoxy proxy (to the open internet). This way we can control which application uses the Tor Network to go online (ex: Tor Browser) or the open internet if necessary (ex: standard Firefox browser).
Which Web browser does ICLOAK use? Are there any special browser customizations?
We use the TorBrowser Bundle as our main anonymous browser based on Firefox ESR. We believe the Tor Foundation did an excellent job at securing it, and we only added our own start up page to better inform the user about their current public IP and exit node location. So our browser has everything the TorBrowser Bundle has such as “HTTPS Everywhere,” “NoScript” and “Torbutton” plugins.
As mentioned before our network controller is what manages Tor and local proxy in an ICLOAK session. The goal of the controller is to easily adjust how any application goes online either now with Tor or open web access, and even VPN, I2P, Freenet, etc. access per application in the near future.
This is an important part of our underlying framework so none of the complex network configuration needs to be dealt with by the user. It also allows us to truly give a CHOICE to the user.
By default the ICLOAK system user has NO network access (or even root access) except for what the network controller makes available to the applications in the platform. This also prevents any privilege escalation and network access. So even if some bad malware got through the open, regular Firefox browser, it would have no way to connect out to exfiltrate data or reach a command and control server for further infection.
Is the ICLOAK software platform open source?
We have not Open Sourced the project yet. We plan to open source everything this year. Additionally, we are currently raising a round of funding and will use part of it do a full third party code audit later this year.
Do you offer a VPN service with the product?
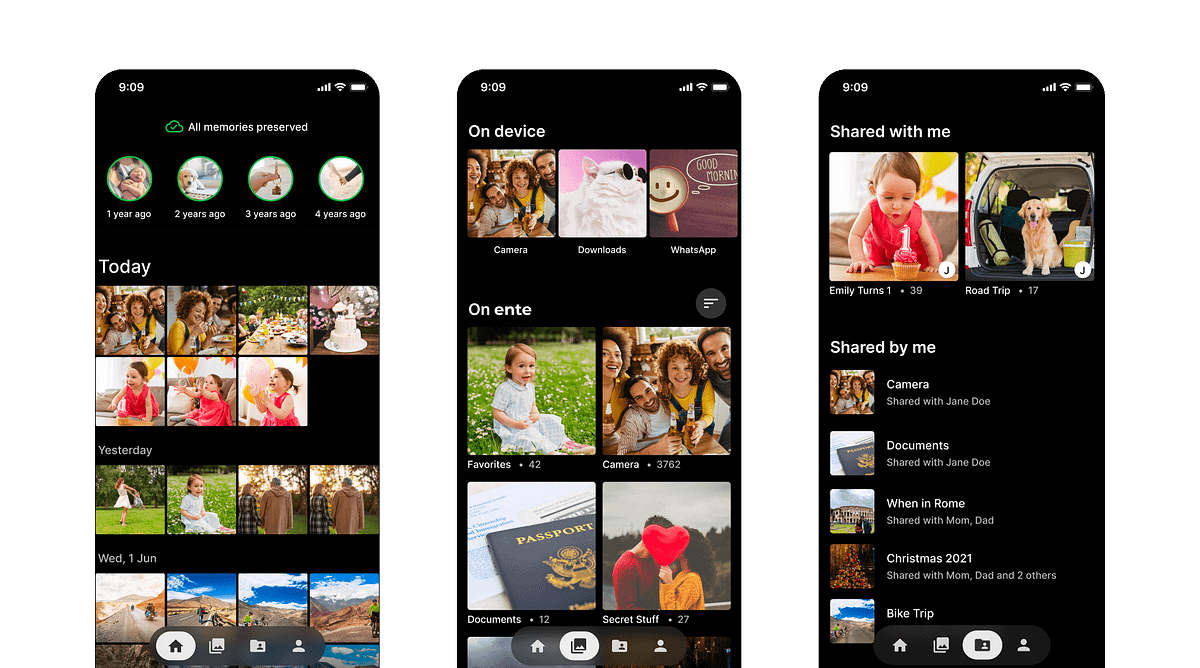
No, there is currently no VPN service. However, we are currently working on one that will be available soon. We are shooting for April of this year. Additionally, we will have some “zero knowledge” encrypted cloud backup and sync features available in Q2.
How will users get new features as they are released?
Because ICLOAK has a great updating platform, new features will become available automatically for users as we deploy them.
The ICLOAK Stik is available at Amazon for $99.