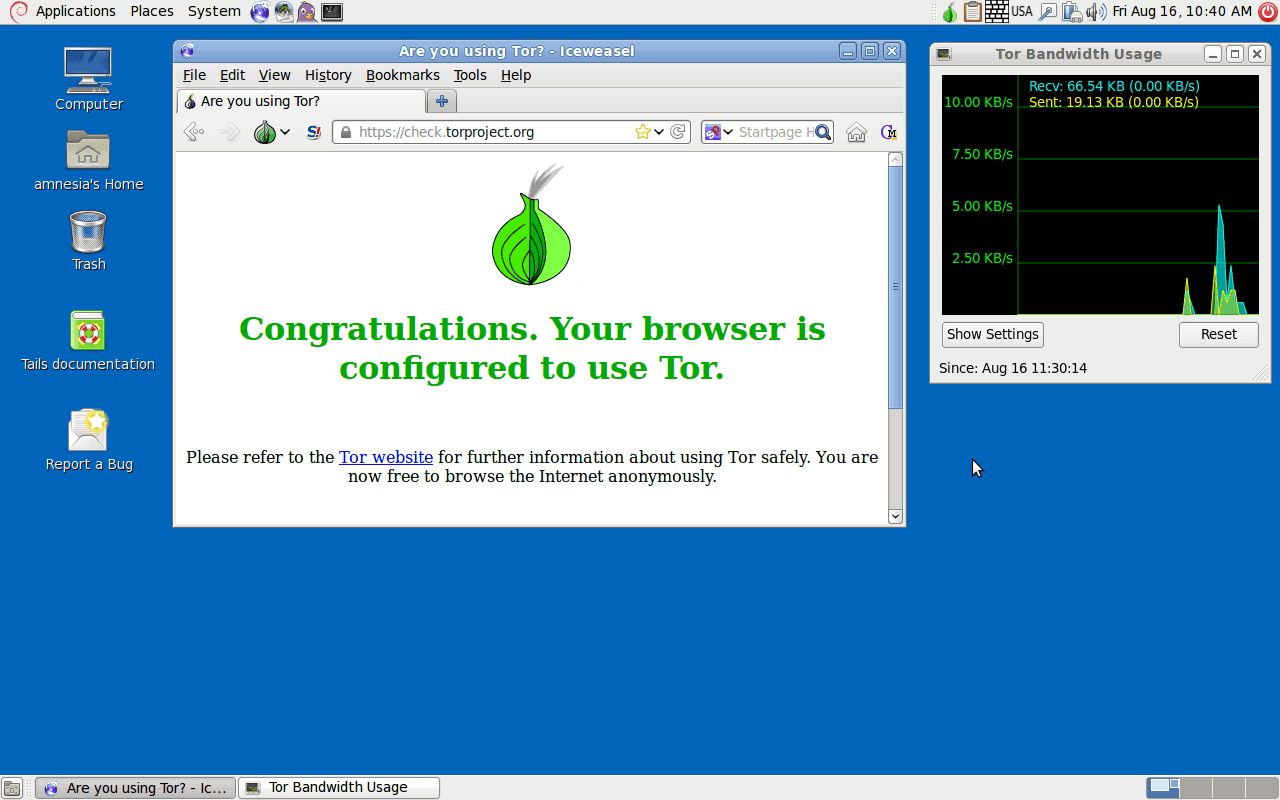
How Does ICLOAK Plug-and-Play Privacy Work?
ICLOAK recently launched its plug-and-play online privacy solution, which is based on a custom Linux distribution that boots from a USB stick. We contacted the company to get a better sense of how exactly its privacy features work, including Tor integration, VPN availability and more. This is what ICLOAK founder Eric Delisle said in response […]
How Does ICLOAK Plug-and-Play Privacy Work? Read More »