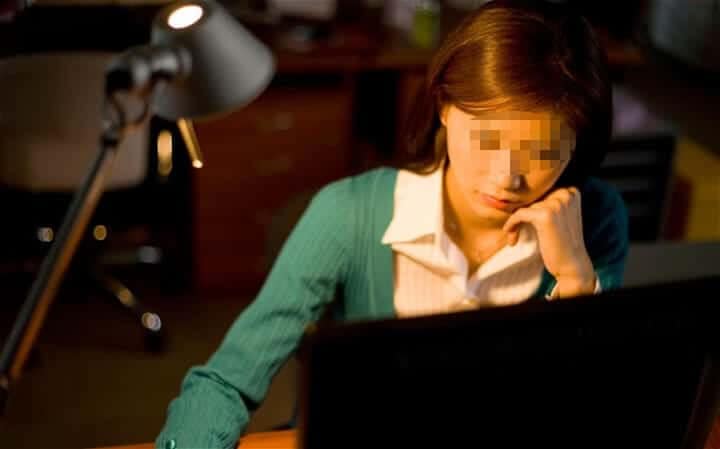
Forrester Report Says Online Privacy is Matters More than Ever
Online privacy will be a defining factor in businesses’ success and failure in 2016. That’s according to new findings from Forrester Research, which says Internet privacy has become more important than ever to consumers. “In 2016, privacy strategy can no longer merely focus on aligning with compliance requirements,” one Forrester representative wrote in summarizing the […]
Forrester Report Says Online Privacy is Matters More than Ever Read More »